Microsoft made a post on the Inside Windows Live blog today alerting users that there is a malicious worm currently trying to spread itself through IM networks, including Windows Live Messenger 2009 (Wave 3). Here’s an excerpt from the post:
A particularly malicious worm (a self-replicating computer virus) is currently trying to spread itself through many of the world’s largest instant messaging and social networks, including Windows Live Messenger 2009 … The worm spreads by inserting a link into an IM conversation with a person whose computer is already infected. When someone clicks the link, it opens in a browser, downloads the worm on the recipient’s computer, and then repeats this process.
Normally, when Messenger sees a web address in a conversation it is turned into a hyperlink which, when clicked, automatically opens in a web browser. This feature makes it very easy for the malicious worm to be unknowingly installed on your computer by clicking on the link and being sent to a web site containing the malicious software.
We’ve temporarily turned off active hyperlinks for web addresses sent in IM conversations using Windows Live Messenger 2009. You will still be able to copy a web address and paste it into a browser window if you know it to be safe.
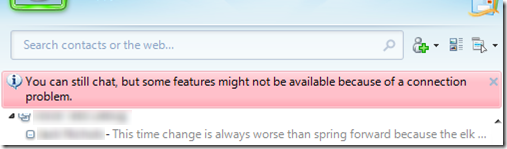
Here’s the warning message you might see when you log in to Windows Live Messenger 2009 today:
Take note that users of the latest Windows Live Messenger 2011 (Wave 4) are not affected thanks to the built-in Microsoft SmartScreen Safety Link feature (the malicious link will be automatically blocked and gives you a warning page). As always, always keep your computer security updates and anti-virus definitions up to date, and exercise caution when someone, including your friends (you’ll never know if their account got compromised or not) sends you a link. If you don’t have anti-virus software installed yet, consider getting the free Microsoft Security Essentials.